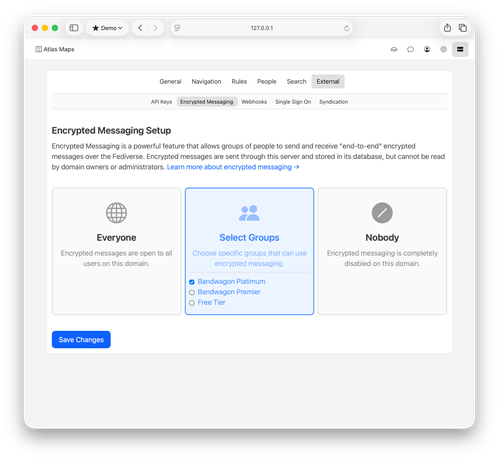
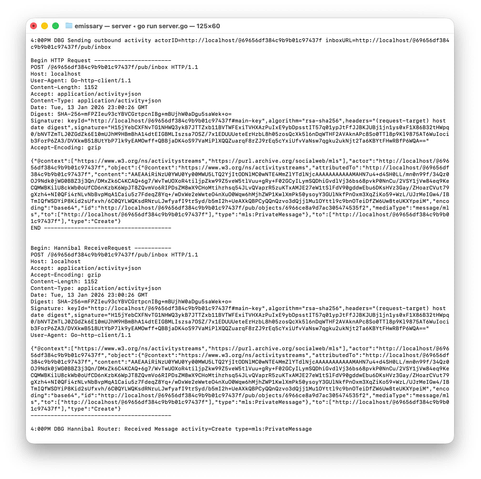
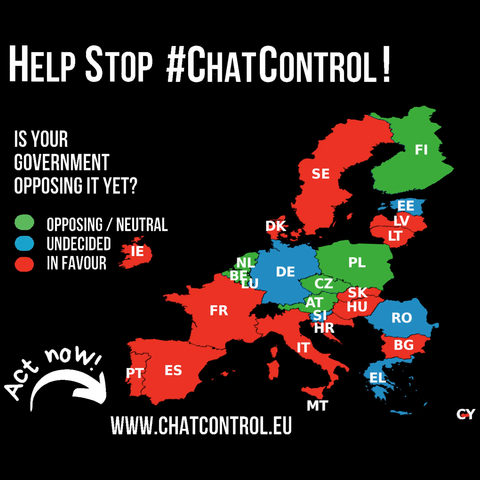
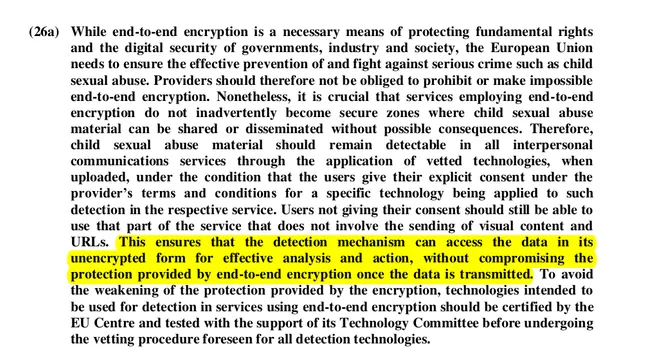
Magical backdoor only for "the good guys" is a complete fantasy 🔑✨
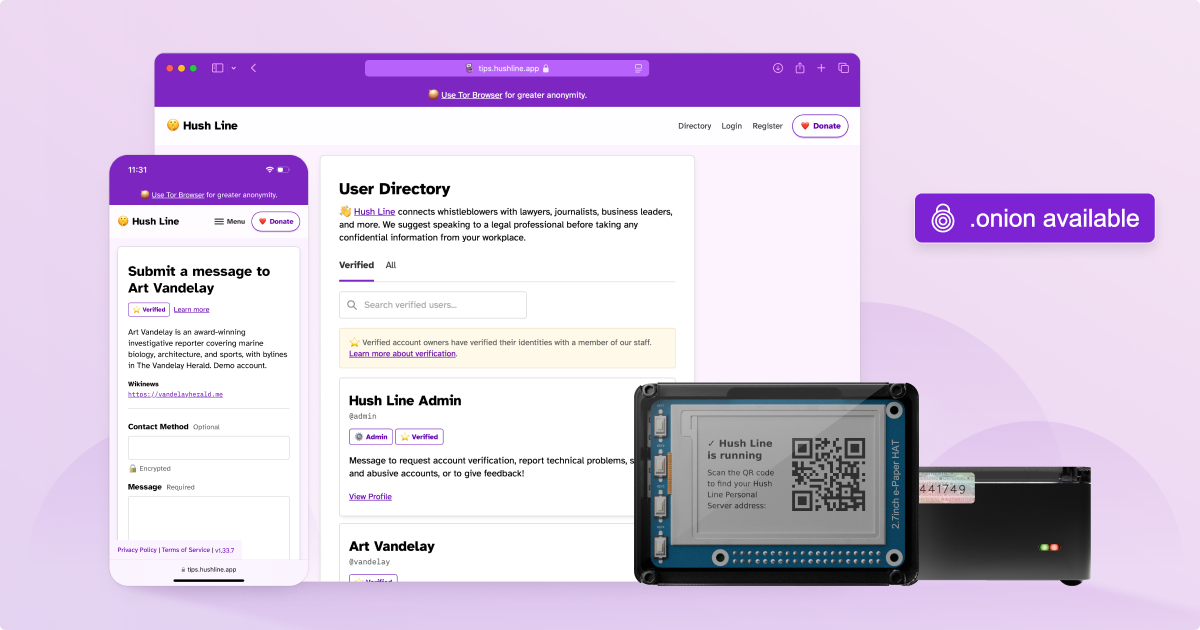
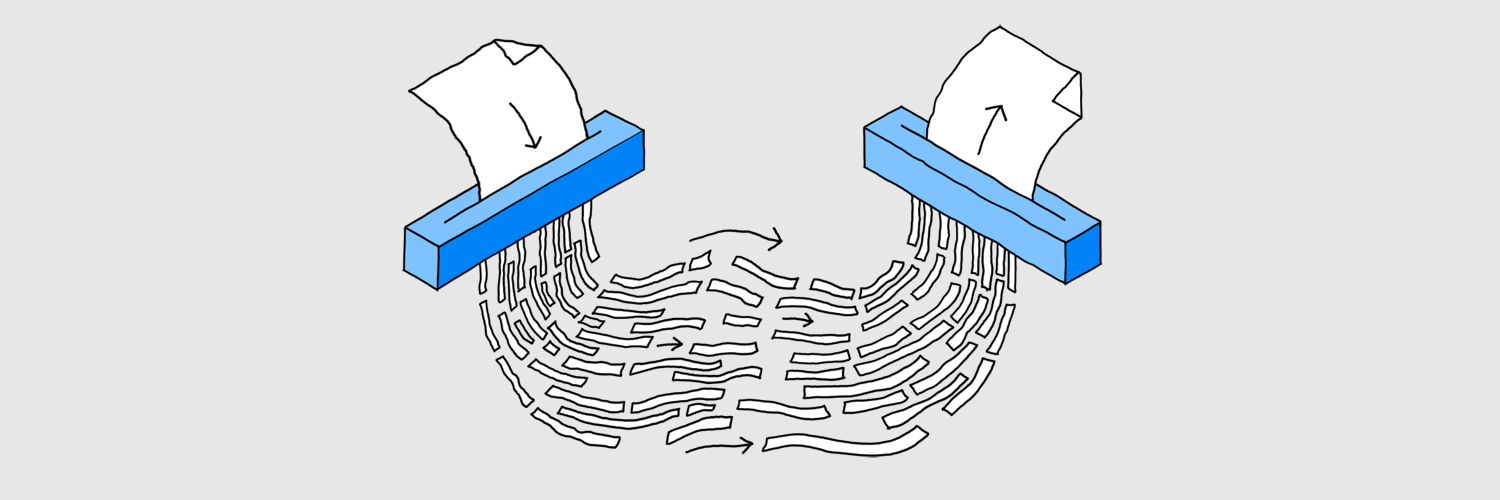
Let's say the strategy is akin to creating a MagicalKey that unlocks every door (a magical key because thinking encryption backdoors would only be used by "the good guys" is a great example of magical thinking).
Imagine only 1000 police officers have MagicalKeys.
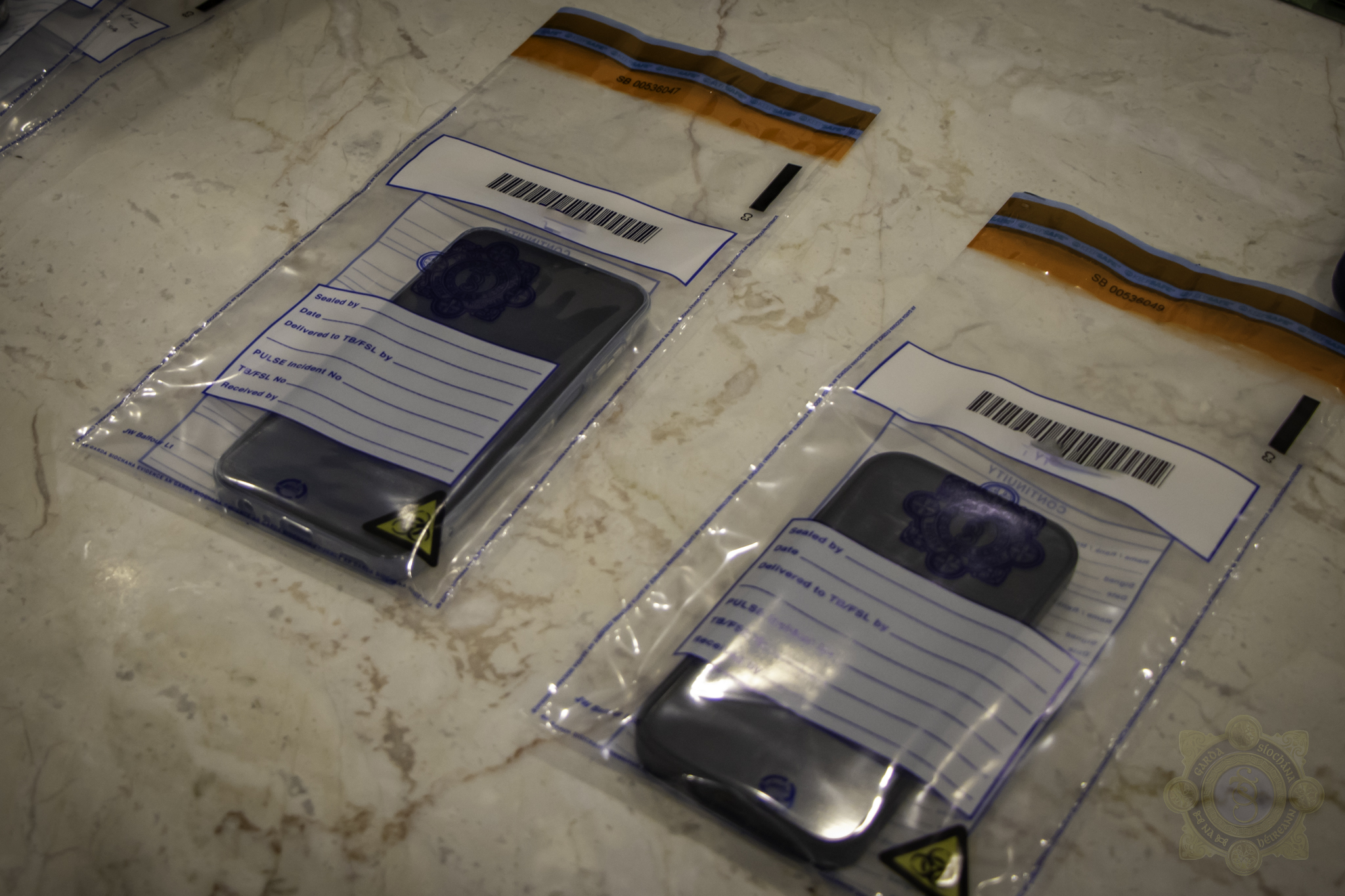
Overtime, let's say only 1% of the police officers accidentally lose their MagicalKey. Now 10 MagicalKeys are lost in the wild and could be used by anyone else, for any purposes, including crime.
Then, let's say only 0.1% of police officers get corrupted by a crime gang. That's just one right? This corrupted "good guy" lets the gang create a double of the MagicalKey. Which crime gang wouldn't want a key that can magically open any door?
Now, the gang creates doubles of the MagicalKey they have. They use it subtly at first to avoid detection. They make sure they never leave traces behind, so victims have no idea their door got unlocked.
During this time, they steal your data, they sell it, they use it to impersonate you, they use it to harm you and your loved ones.
Then, another criminal figures out on their own how to emulate a MagicalKey without even having access to one.
The criminal creates a reproducible mold for this Emulated-MagicalKey and sells it to other criminals on the criminal market. Now, the MagicalKey™️ is available to any criminals looking for it.
Restrictions on the backdoor are off. Your personal data is up for grabs.
This is what is going to happen if backdoors are implemented in end-to-end encryption. But don't worry they say, "it's only for the good guys!".
At least, the criminals' data will also be up for grabs, right?
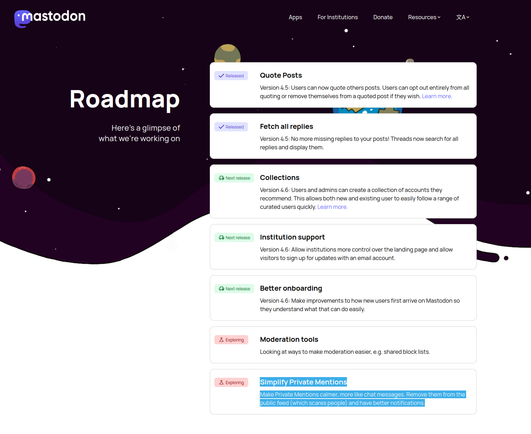
Nope! The criminals knew about this, so they just started using different channels that weren't impacted.
Criminals will have their privacy intact, they don't care about using illegal tools, but your legal privacy protections will be gone.
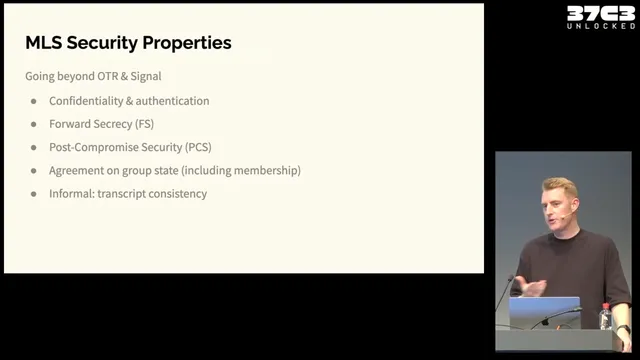
Backdoored end-to-end encryption isn't end-to-end anymore, it's just open-ended encryption. This offers pretty much no protection at all.
Extract from: https://www.privacyguides.org/articles/2025/04/11/encryption-is-not-a-crime/
#Privacy #Encryption #E2EE #RootForE2EE
























 💙👇
💙👇









































/cdn.vox-cdn.com/uploads/chorus_asset/file/24008017/acastro_STK085_Telegram_02.jpg)